If you've spent any time in the security industry lately, you've probably heard some version of the same statistic: there are millions of unfilled cybersecurity jobs, and the number keeps growing. It's become a kind of background noise — repeated at conferences, cited in vendor whitepapers, used to justify everything from hiring freezes to six-figure training budgets.
But what does the data actually say in 2026? And more importantly, is the problem really about a shortage of people — or something else entirely?
Let's dig in.
The Numbers Are Real — But They're Telling Only Half the Story
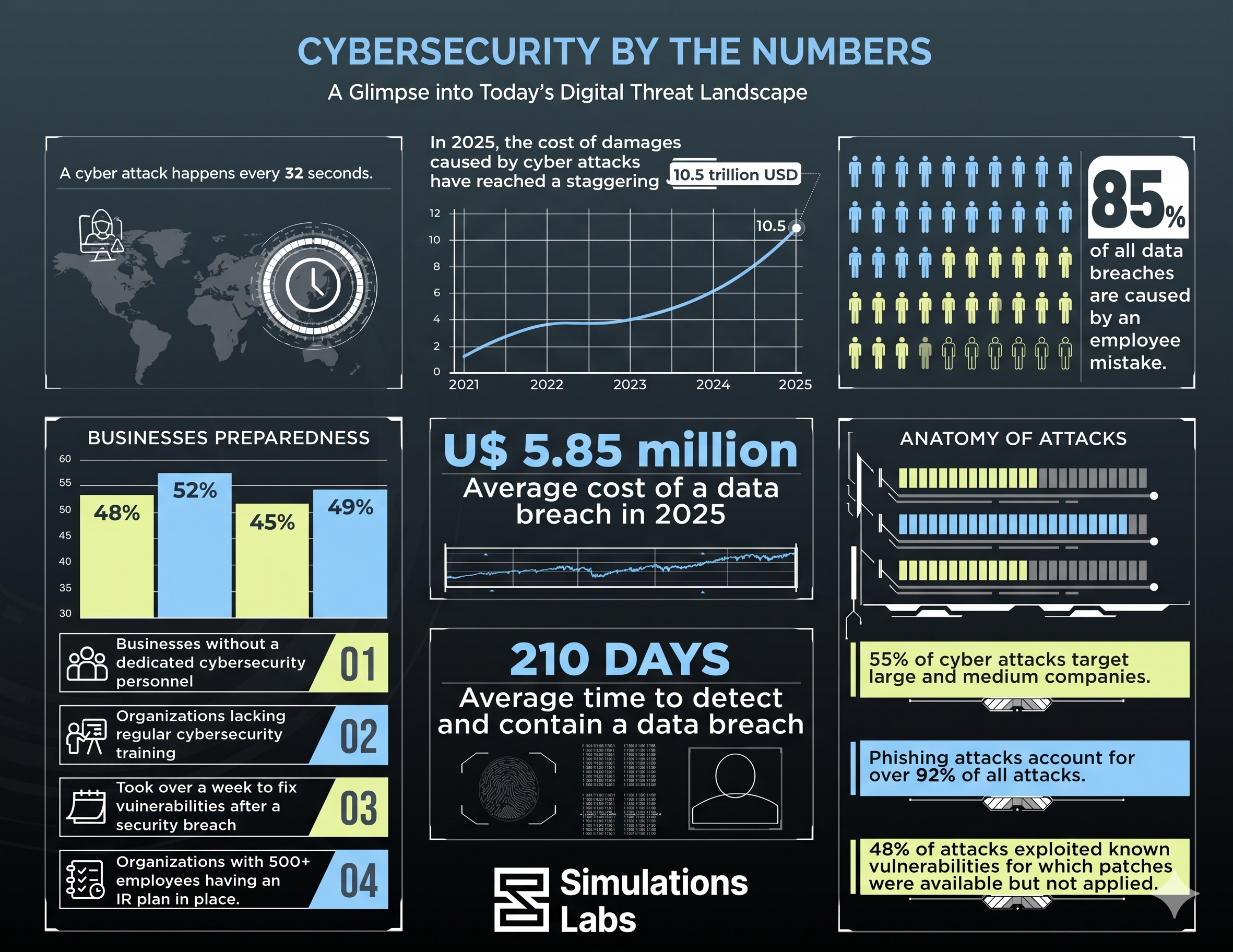
The most commonly cited figure comes from (ISC)² and similar bodies: roughly 3.4 to 4 million cybersecurity professionals are needed globally to close the workforce gap. That number has been climbing for years. On the surface, it paints a picture of an industry in crisis mode.
But here's what those headlines often miss: the shortage isn't evenly distributed. It clusters hard in specific roles, specific regions, and specific experience levels. Entry-level security analysts, for instance, are not actually that scarce — there's a healthy pipeline of people trying to break into the field. What's genuinely scarce is mid-to-senior talent with hands-on, demonstrable skills in areas like cloud security, threat hunting, OT/ICS security, and incident response.
There are thousands of people with security certifications who struggle to land their first job. Meanwhile, experienced red teamers and cloud security architects with real-world skills can name their price and still get multiple offers in the same week. That's not a shortage of people. That's a skills distribution problem.
What "Skills" Actually Means in 2026
The definition of "cybersecurity skills" has shifted dramatically over the past few years. Five years ago, knowing your way around a SIEM and being able to interpret firewall logs was enough to get hired as an analyst. Today, organizations are dealing with:
-
Attack surfaces that span multi-cloud, hybrid, and edge environments
-
Adversaries using AI-assisted tooling to move faster than traditional defenses
-
Regulatory environments (NIS2, DORA, SEC disclosure rules) that require security teams to also be fluent in compliance
-
A growing expectation that defenders understand how attacks actually work — not just how to read about them
That last point is where the skills gap bites hardest. Hiring managers consistently say the same thing in surveys and in conversation: they don't just want people who know the theory. They want people who've actually done the thing. Who've exploited a vulnerable machine. Who've had to pivot through a network under pressure. Who knows what a lateral movement pattern looks like because they've executed one in a lab environment.
That's a fundamentally different bar than passing a multiple-choice certification exam.
The Hiring Pipeline Problem
Part of what's driving the perception of a skills gap is that traditional hiring pipelines weren't built for the type of talent organizations now need.
University cybersecurity programs are improving, but many still emphasize theory over practice. Bootcamps have proliferated, but their quality varies wildly. Certifications remain the default credentialing mechanism even though they often don't test what actually matters on the job.
The result: employers post job requirements that are unrealistic (five years of experience with a tool that's been around for three years, anyone?), and candidates who genuinely have the skills can't demonstrate them in a way that survives the resume-screening process.
We're essentially in a situation where the industry needs plumbers, we're testing for plumbers by asking them to describe water, and then wondering why all the pipes are leaking.
.png)
The Demographic Picture Isn't Getting Simpler
The skills gap also has a diversity dimension that doesn't get enough attention. The cybersecurity workforce remains heavily skewed toward certain demographics, certain educational backgrounds, and certain career trajectories. That means the industry is drawing from a much smaller talent pool than it could be.
People who came up through non-traditional paths — self-taught hackers, CTF competitors, folks who pivoted from IT support or network admin — often have the most practical skills and the most creative problem-solving instincts. But they're frequently filtered out by hiring processes that weren't designed with them in mind.
Closing the skills gap isn't just about training more people. It's about building pathways that recognize practical competence wherever it comes from.
What Actually Works: Skills-First, Practice-First
The organizations making real progress on the skills gap share a few things in common.
First, they've moved toward competency-based hiring. Instead of treating certifications as a proxy for ability, they assess candidates through practical challenges — CTF-style exercises, simulated incident response scenarios, and technical interviews that involve actually doing something rather than just describing it.
Second, they've invested in continuous skills development rather than one-off training. Cybersecurity isn't a field where you learn it once and you're done. Threats evolve, platforms change, and new attack techniques emerge constantly. Teams that stay sharp are the ones that practice regularly — through internal CTF competitions, cyber drills, and hands-on lab environments.
Third, they've broadened the definition of "qualified." Some of the best SOC analysts, penetration testers, and threat hunters in the industry don't have a four-year degree in computer science. They have years of practical experience, a track record of solving real problems, and the habit of continuously sharpening their skills.
How CTFs and Hands-On Training Are Closing the Skills Gap
One of the biggest trends helping reduce the cybersecurity skills gap in 2026 is the rapid growth of hands-on training platforms, CTF hosting environments, and cyber ranges. Organizations are increasingly prioritizing candidates who can demonstrate practical cybersecurity skills instead of relying only on theoretical knowledge or certifications.
Platforms like TryHackMe, Hack The Box, and CyberTalents have become widely used for developing offensive and defensive cybersecurity skills through real-world scenarios. These platforms provide guided labs, vulnerable machines, attack simulations, and role-based learning paths covering areas such as penetration testing, SOC operations, cloud security, malware analysis, digital forensics, and threat hunting.
At the same time, platforms such as CTFd and Simulations Labs have made it easier for universities, enterprises, governments, and cybersecurity communities to host Capture The Flag (CTF) competitions at scale.
The Bottom Line
The cybersecurity skills gap is real, but it's not primarily a headcount problem. It's a skills-distribution problem, a hiring-process problem, and a practice-gap problem all tangled together.
The organizations that will win — both employers trying to hire and professionals trying to get hired — are those that take practical skill-building seriously. That means moving beyond passive learning and into environments where you're actually under pressure, actually making decisions, and actually building the kind of muscle memory that matters when something goes wrong at 2 am.
Because that's when the skills gap stops being a statistic and becomes very, very real.
Simulations Labs helps organizations run CTF competitions, cyber ranges, and hands-on training simulations — building the kind of practical skills that actually close the gap.