It usually starts the same way. Someone stumbles into their first Capture the Flag competition — maybe through a university club, maybe through a Discord server, maybe just because they were bored one weekend and found one online. They get introduced to picoCTF or CTFD or Simulations Labs or CyberTalents. They have no idea what they're doing. They spend four hours on a challenge that most people solve in twenty minutes. They get stuck in ways that feel embarrassing.
And then something clicks. They solve something. Or they read a write-up after the competition ends and realize they were closer than they thought. And they come back.
That cycle — get stuck, figure it out, come back — is how a huge percentage of working cybersecurity professionals got their start. And in 2026, the path from CTF hobbyist to a paid security career is more navigable than it's ever been. But it's not automatic. You have to be intentional about it.
Here's what that path actually looks like.
Why CTFs Are a Legitimate Career Launchpad
Before getting into specifics, it's worth being direct about something: CTF competitions are not a gimmick or a toy. The skills you build through competitive hacking challenges map directly onto real security work.
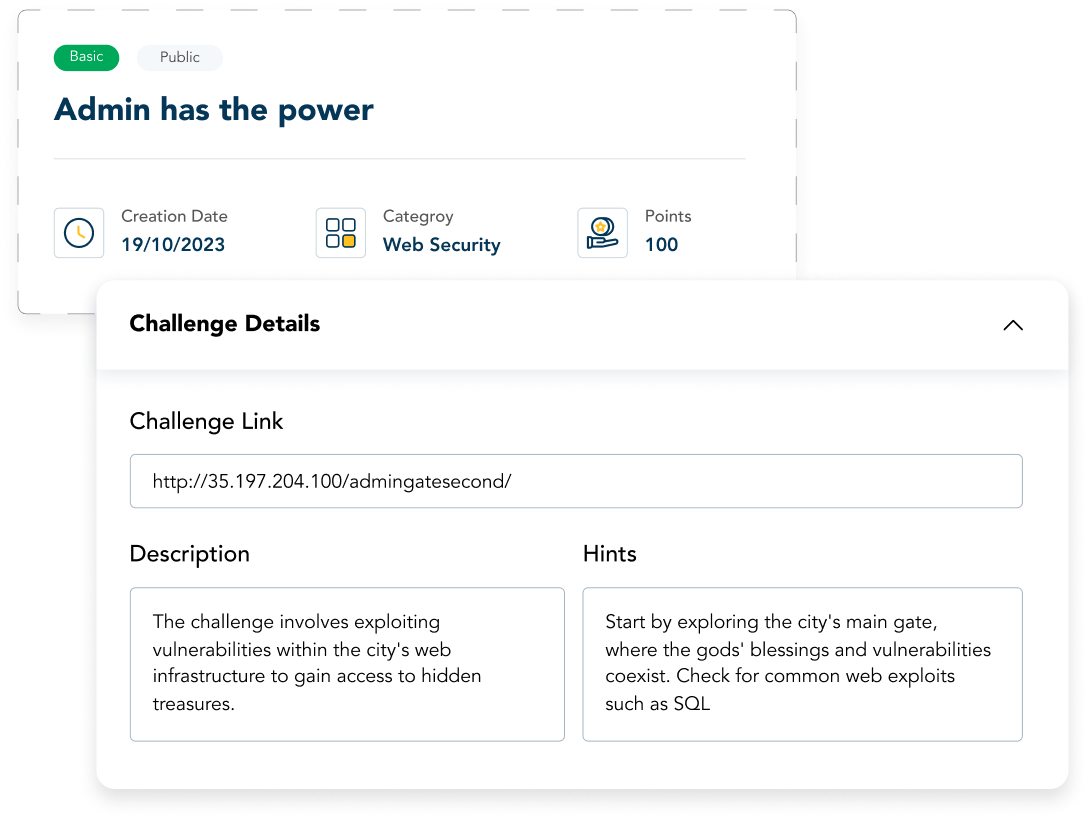
Web exploitation challenges teach you how applications fail — SQL injection, XSS, SSRF, and authentication bypasses. Binary exploitation teaches you how memory works at a level that most developers never touch. Forensics challenges teach you to read artifacts, reconstruct events, and think like an investigator. Cryptography challenges force you to actually understand the math that underpins secure systems, not just trust that it works.
The transfer to professional work isn't perfect — CTF environments are artificial in ways that real environments aren't. But the core skills, the methodology, the problem-solving instincts — those are absolutely real. Hiring managers who work in security know this. A strong CTF track record is meaningful on a resume in a way that a lot of other credentials aren't.
What the Career Paths Actually Look Like
The path from CTF competitor to security professional isn't one road. It branches depending on what you enjoy, what you're good at, and what the market needs. Here are the most common trajectories:
SOC Analyst (and the Blue Team Path)
This is the most accessible entry point and where a lot of CTF players land first. SOC analysts monitor environments for threats, investigate alerts, and triage incidents. The work is a mix of pattern recognition, technical investigation, and communication.
CTF skills that transfer: forensics, log analysis, and network traffic analysis. The forensics and network categories in most CTFs are essentially SOC work in challenge form. If you're good at them, you have a genuine head start.
The gap to bridge: CTFs don't always teach the tool stack that enterprises actually use — SIEM platforms, EDR tooling, ticketing systems. Supplement your CTF practice with hands-on time in common tools. Many have free tiers or learning environments.
Timeline: With solid CTF experience and focused preparation, landing a junior SOC role within 12-18 months of serious effort is realistic for most people.
Penetration Tester / Red Teamer
This is the role most people imagine when they think about "hacking for a living." Penetration testers are paid to attack systems — to find vulnerabilities before malicious actors do.
CTF skills that transfer: web exploitation, binary exploitation, privilege escalation, and network pivoting. Offensive CTF categories are essentially entry-level pentesting in challenge form. People who dominate offensive CTF categories often make extremely strong pentest candidates.
The gap to bridge: Real pentesting requires a methodology and report-writing skills that CTFs don't teach. You're not just finding the flag — you're documenting what you found, explaining the business risk, and recommending fixes. Getting some experience writing technical reports, even informal ones, helps.
Also, certifications matter more here than in other paths. OSCP (Offensive Security Certified Professional) remains the gold standard for entry-level pentesters and is worth pursuing. It's a practical exam — you actually hack machines — which means your CTF experience translates directly.
Threat Intelligence Analyst
Threat intelligence is less about hands-on technical work and more about understanding the adversary landscape — who's attacking whom, with what tools, for what purposes. It sits at the intersection of security and research.
CTF skills that transfer: OSINT challenges, reverse engineering, malware analysis. If you're the type of CTF player who finds yourself going deep on attribution questions and researching threat actor techniques, this might be your lane.
The gap to bridge: Threat intelligence requires broader contextual knowledge — geopolitics, criminal ecosystems, industry-specific threat landscapes. Supplement technical practice with reading: threat intel reports from vendors like Mandiant, Recorded Future, and CrowdStrike are publicly available and worth your time.
Malware Analyst / Reverse Engineer
This is one of the more specialized paths, and it's not for everyone — but for people who love binary challenges and the puzzle of understanding how software works at the lowest level, it's deeply satisfying work.
CTF skills that transfer: Reverse engineering challenges are directly applicable. If you've spent time in Ghidra or IDA Pro working through CTF binaries, you already have the core muscle.
The path: Many malware analysts start as SOC analysts or threat intelligence analysts and move into malware work as they develop expertise. It's less common to land directly in a malware analysis role without some prior professional security experience.
Practical Steps to Bridge the Gap
Knowing the destination is one thing. Getting there requires a plan. A few things that consistently make a difference:
Compete consistently, not just occasionally
One CTF won't build a career. A pattern of regular participation — across multiple competitions, across multiple categories — builds the kind of depth that shows up in interviews. Aim for 10-15 competitions a year minimum. That's roughly one every few weeks, which is very achievable with the number of events available online.
Write up your solutions
This is the step most people skip and the one that pays off most. After every competition, write up your solutions — not just the flags, but your reasoning, your methodology, where you got stuck, and why. Post them publicly.
Write-ups serve two purposes. They reinforce your own learning by forcing you to articulate what you did. And they become a portfolio — a searchable, public record of how you think and what you can do. Hiring managers who know what to look for will find them.
Move from CTF to more realistic environments
CTFs are a great starting point, but the best preparation for professional work involves environments that simulate real organizational setups — Active Directory networks, cloud environments, and complex multi-machine scenarios.
Several platforms offer this kind of more realistic training. The jump from CTF-style challenges to enterprise simulation is where a lot of people get stuck, so crossing that gap deliberately is important.
Get involved in the community
The cybersecurity community is genuinely collaborative in a way that a lot of industries aren't. Discord servers, local chapters, CTF teams — the relationships you build there lead to referrals, mentors, and job opportunities that never show up on a job board.
If you're not already part of a CTF team, find one or build one. Working through challenges with other people accelerates your learning and expands your network simultaneously.
One Thing Worth Saying Directly
The path from CTF hobbyist to security professional is real, and it's traveled by a lot of people every year. But it's not passive. It doesn't happen because you've played a lot of CTFs — it happens because you've been intentional about building the specific skills that professional work requires, you've documented your journey in a way others can evaluate, and you've put yourself in front of the right opportunities.
The skills gap in security is real. Organizations are actively looking for people who can do the work. The question is whether you can demonstrate that you're one of them.
CTFs are an excellent way to build that proof.
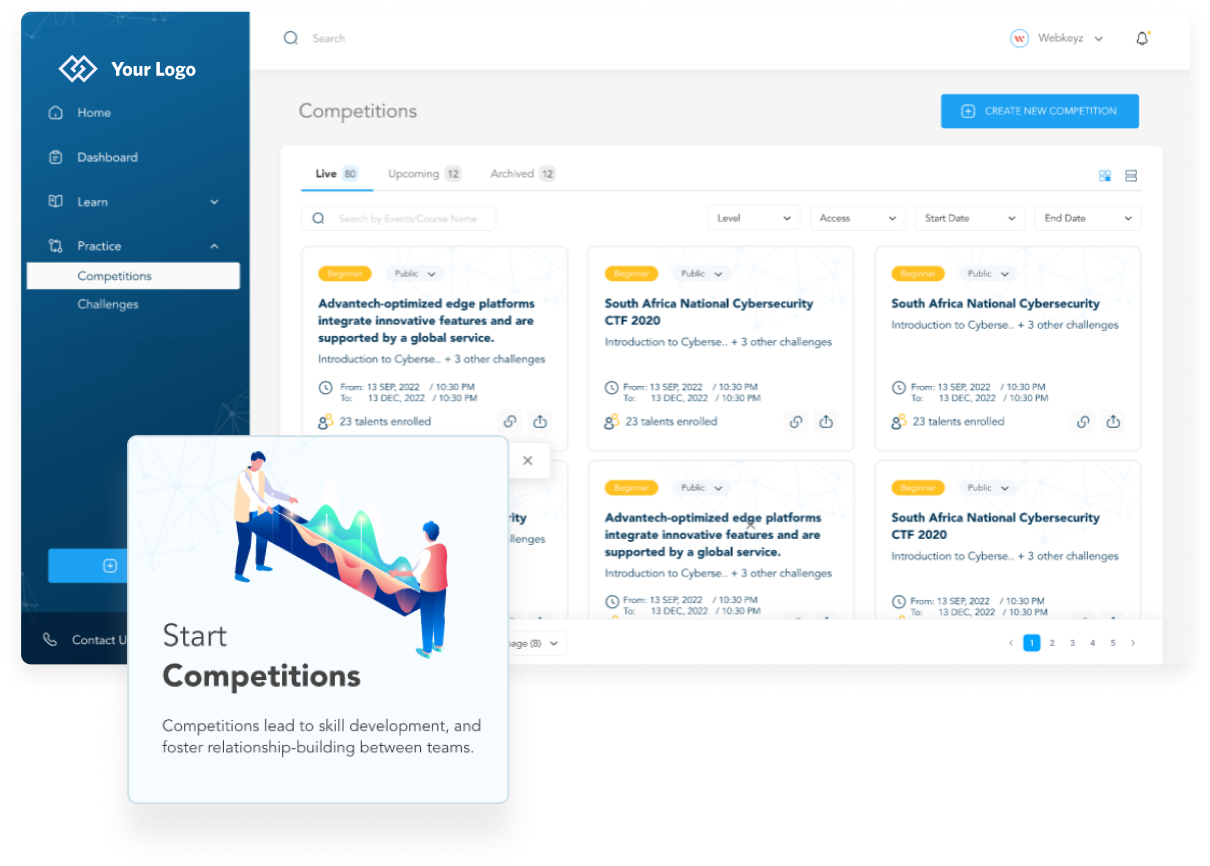
Simulations Labs provides a platform for hosting and competing in CTF competitions and cyber simulations — for individuals looking to build skills and for organizations looking to find and develop talent. With a library that has over 200 expert-created challenges, hosting CTFs has never been easier.