Ten Years of Building the Simulations No One Wanted to Build Article 1 of 3 — The Simulations Labs Challenge Library
The Work Behind Good Cybersecurity Training
This is the first article in a three-part series about how Simulations Labs helps cybersecurity program leaders, instructors, and team leads build better training — faster. In this article, we’ll introduce the challenge library: what it is, how it was built, and why it matters. In the second article, we’ll explore the gap that even a large, well-organized library creates — and why finding the right content is harder than it sounds. In the third, we’ll go under the hood of the Simulations AI Copilot: the tool built specifically to solve that problem, and how it works in practice.
There’s a question that comes up in almost every conversation about cybersecurity education, whether you’re running a university program, leading a security team, or building a community competition. The question isn’t ‘should we do hands-on training?’ Everyone agrees on that. The question is: where does the content actually come from?
Building a realistic cybersecurity simulation from scratch is not a small job. You need a scenario that mirrors how attackers actually behave. You need a technical environment that holds up under real hacking attempts. You need difficulty calibration, flag logic, writeups, and metadata so the right learners find it. Then you need to maintain it as the threat landscape changes. It takes time, expertise, and resources that most organizations — even large ones — would rather spend elsewhere.
That's the problem Simulations Labs has been quietly solving for over a decade.
What the Library Actually Is
Simulations Labs started as a platform for running CTF competitions — Capture the Flag events where participants solve cybersecurity challenges to earn points and demonstrate skills. Over the years, that meant building challenges. Lots of them. And not just any challenges: ones that were technically sound, professionally designed, and varied enough to serve the full spectrum of cybersecurity disciplines.
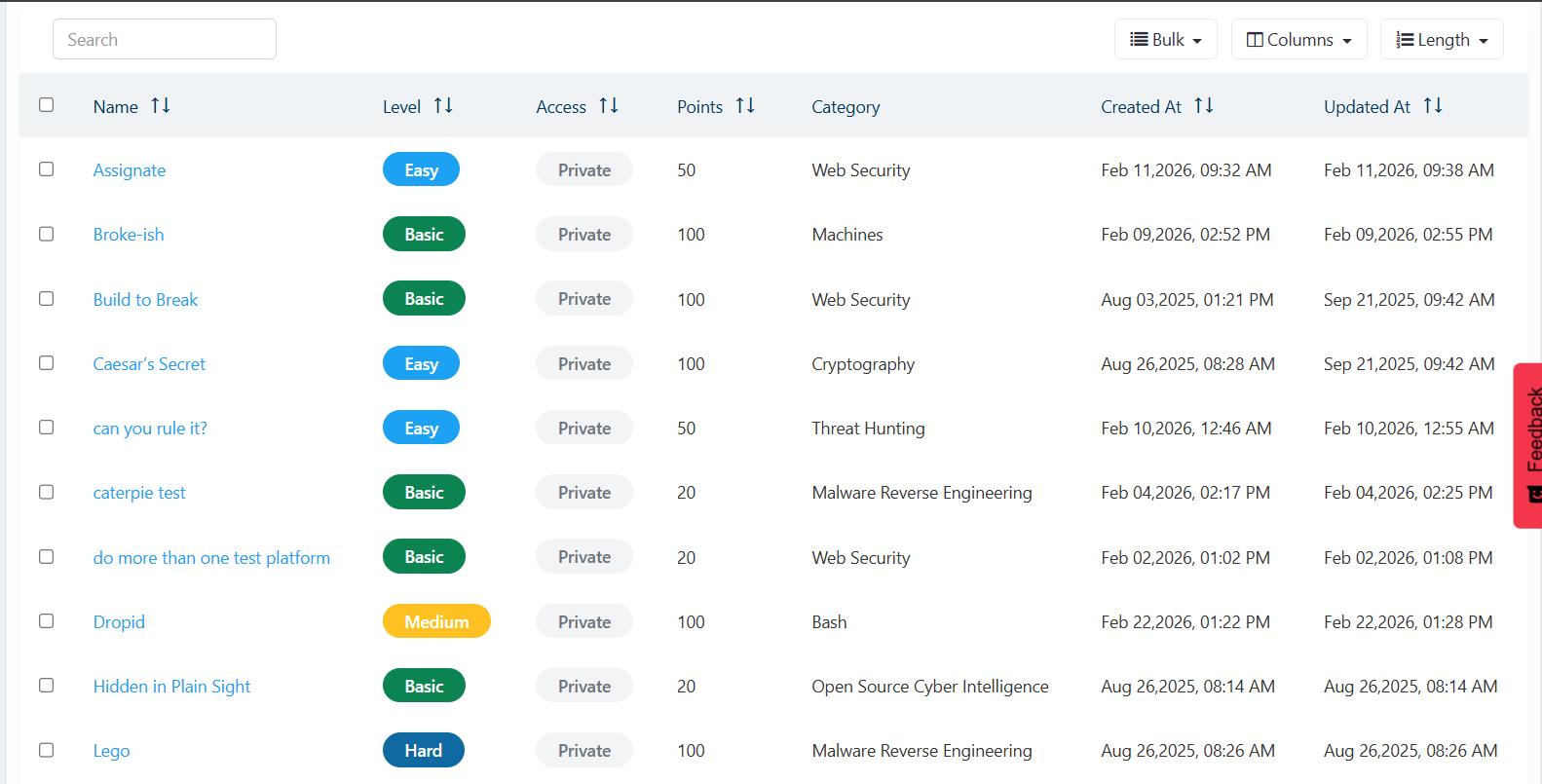
Today, that accumulated work has become a library of more than 2,100 challenges. It spans web security, network exploitation, cryptography, digital forensics, incident response, reverse engineering, cloud misconfigurations, and more. Each challenge is a self-contained simulation — a realistic scenario with a technical environment, a defined objective, and a measurable outcome. Some are designed for beginners, finding their footing. Others are genuinely difficult, built to push experienced practitioners into unfamiliar territory.
The breadth is deliberate. Cybersecurity is not one skill. It's a constellation of disciplines that overlap in some places and diverge sharply in others. A SOC analyst, a penetration tester, and a forensic investigator all work in the same field, but they need to develop very different instincts. A library that only serves one profile eventually stops being useful to everyone else.
Why This Matters to Instructors and Program Leaders
The instructors and cybersecurity leaders who use Simulations Labs are not, in most cases, looking for a lecture platform. They already know how to deliver content. What they struggle with is the raw material — scenarios that feel real, that test the right things, and that can be deployed without weeks of preparation.
Building a curriculum from scratch when you also have to teach, manage a team, or run an organization is simply not practical. The Simulations Labs library changes the starting point. Instead of a blank page, you start with access to a decade's worth of professionally built scenarios. You pick what fits, configure how it's delivered, and focus your energy on the teaching — not the construction.
Instead of a blank page, you start with access to a decade's worth of professionally built scenarios.
This is why the library is used by university professors building semester-long cybersecurity curricula, by enterprise security teams creating internal upskilling tracks, and by community leaders running public competitions and learning events. The use cases are different, but the underlying need is the same: quality simulation content, ready to go.
The Three Ways People Use the Content
Pre-existing library access
Organizations can draw directly from the library to populate their CTF events or training programs. Challenges are categorized, tagged, and difficulty-rated so program leads can curate a set that fits their specific goals without reviewing every option manually.
Custom content creation
For teams with unique requirements — a very specific technology stack, a particular regulatory scenario, a company-branded experience — Simulations Labs builds bespoke challenges that match exactly what's needed. The library serves as a foundation; custom content extends it.
Hybrid programs
Most serious training programs end up using both. A core track built from existing challenges, supplemented by custom scenarios that address particular skill gaps or organizational contexts. The platform supports both seamlessly, through the same interface.
.png)
What Ten Years of Building Actually Produces
It's easy to say 'we have 2,100 challenges' without that number meaning much in context. So here's what it actually represents.
It means that when an instructor wants a web security track that progresses from basic authentication bypass to complex business logic vulnerabilities, that track exists. It means that when a company wants to put their security team through a forensic investigation scenario that mirrors a realistic incident — memory dump analysis, log correlation, artifact recovery — there are multiple options to choose from at different difficulty levels.
It means that a community organizer running a competition for participants ranging from curious beginners to working professionals can find appropriate challenges for every skill tier without having to invent anything.
Perhaps most importantly, it means that the scenarios are maintained. The threat landscape changes. Techniques that were advanced two years ago become expected knowledge today. The Simulations Labs library grows and evolves continuously, not as a side project, but as the core of what the company does.
What Comes Next
Having a library this size raises a different kind of challenge. Once you have 2,100 options, how does anyone find the right one quickly? How does a program leader with a specific training goal — a particular role, a specific difficulty, a defined set of techniques — get from that goal to the right scenario in minutes rather than hours?
That's the question we'll dig into in the next article. The short version: this is exactly the kind of problem that AI is well-suited to solve. And Simulations Labs has built something specifically designed to close that gap.
But that starts here — with ten years of building something worth finding.
Read the Next Article Now
The Gap Nobody Talks About in Cybersecurity Training